Agenda
Download Brochure
Flip through our 2024 conference brochure and discover what’s new this year.
Day 1
May 15, 2024
Registration and Continental Breakfast
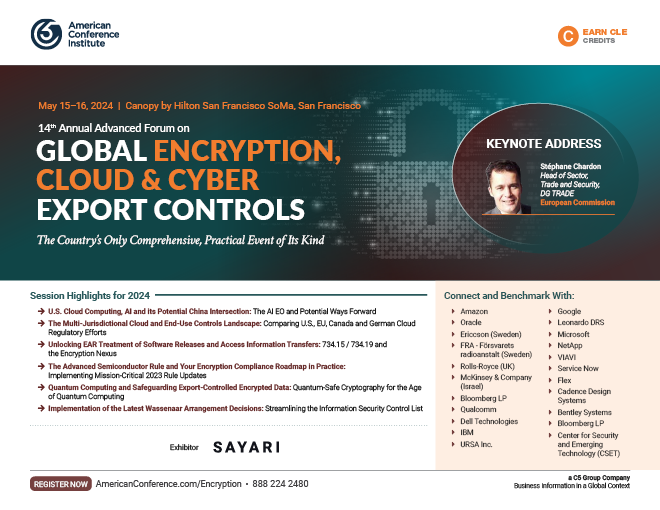
The Future of U.S. Cloud Computing, AI and its Potential China Intersection: The AI EO and Potential Ways Forward for Managing U.S. Technology Security Export Risks

Shiva AminianPartnerAkin Gump Strauss Hauer & Feld LLP

Jacob FeldgoiseData Research AnalystCenter for Security and Emerging Technology (CSET)

Alan Martin HayesSenior CounselOpenAI

Lillian NorwoodSenior Manager, Global Trade ComplianceAmazon
- The AI EO: Cloud-specific details, including the cloud ”Infrastructure as a Service” provisions
- Impact of Chinese Generative AI Rules on U.S. AI regulatory efforts
- When Chinese users can still access controlled chips (ECCN 3A090) through clouds services and how to address this
- Anticipating U.S. government restrictions on sale of cloud services to China
Extended Networking Break
CASE STUDY
A Behind the Scenes Look at Implementing the Advanced Semiconductor Rule and Strengthening Compliance

Bob BowenExport and Trade Compliance CounselServiceNow

Melissa DuffyPartnerFenwick & West

Per SundstromHead of Trade Compliance TechnologyEricsson (Sweden)
- Implementing licensing requirements
- Updating licensing policies and Temporary General Licenses
- Gap analysis: Strengthening compliance programs to make sure legal, engineering, and trade compliance are all in the loop with new controls
HYPOTHETCIAL SCENARIOS
Putting Your Encryption Compliance Roadmap into Practice: How to Resolve the Most Complex Advanced Semiconductor Classification and October 2023 Rule Challenges

Hector RiveraDirector, Export and Sanctions ComplianceQualcomm Technologies Inc.

Brian FalboSenior CounselDell Technologies LLC
- Applying licensing requirements for items controlled under ECCNs 5A002 or 5D002 that meet or exceed the performance parameters of the new ECCNs 3A090 or 4A090
- Applying licensing requirements for mass market encryption hardware and software items controlled under ECCNs 5A992 or 5D992
- Restrictions on US persons activities: US persons (citizens, permanent residents, asylees, and refugees) that support the development or production of integrated circuits (IC’s) in China now requires a license
- What kind of ICs are involved?
- What ECCNs are relevant?
- Are any license exceptions available?
- New foreign direct product rules focused on otherwise uncontrolled foreign-origin content for advanced computing and supercomputer-related applications in China
- Expanded “Entity List FDP Rule” (§ 734.9(e)(2)
- New “Supercomputer FDP Rule” (§ 734.9(i)
- New “Advanced Computing FDP Rule” (§ 734.9(h)
Networking Luncheon
The Multi-Jurisdictional AI and Cloud Computing Controls Landscape: Contrasting EU, Canadian, and German Cloud Computing Regulatory Efforts and the Key Differences with U.S. Requirements

John W. BoscariolPartnerMcCarthy Tétrault LLP (Canada)

Lothar DetermannPartnerBaker & McKenzie LLP

Alison Stafford PowellPartnerBaker & McKenzie LLP

Stephan MuellerPartnerOppenhoff (Germany)
- The EU AI Act:
- The changes it will require from AI companies: How soon will they take effect?
- How the Act divides its rules on the level of risk an AI systema
- Will the Act stifle technological innovation?
- Defining DIGITALEUROPE EU export control guidelines vs. U.S. requirements:
- The definition of “export” when encrypted technology is sent outside of the EU
- The definition of software “exports” when the software is provided as a service (SaaS)
- Should an “export” occur when administrators (e.g., at a telecom, cloud service, or SaaS provider) have access to user data for purposes of providing, supporting, or maintaining the service?
- Government of Canada cloud controls:
- Performing security categorization: Attributing “High Watermark” risk profiles of cloud security
- Cloud security control profile selections
- Determining scope of security responsibility for various cloud service models
- Performing security assessments
- Germany:
- Pushback towards EU AI Act around “foundation models”
- The BAFA guidance
- Bitkom’s position
- BAFA guidance vs. EU Dual Use regulation
- Suggestions concerning potential coordination between ANS and Bitkom
Networking Break
Managing the Real-Life Business Impacts of the October 2023 U.S. Advanced Computing and Semiconductor Rule: Practical Insights on Encryption Compliance the Supply Chain Path Ahead

Winnie LukSenior Trade Compliance ManagerOracle

Ajay KuntamukkalaPartnerHogan Lovells
What are the short and long-term computing supply chain impacts of BIS’ latest October 2023 rule covering semiconductors and supercomputing technology? How do the 2023 updates raise the compliance bar? How do they impact encryption compliance? As with any complex and novel export control rule involving innovative technologies and supply chains, many anticipate that the new rules will likely have unintended consequences. Might the controls backfire without buy-in from foreign partners and allies?
This panel of experts will address the future of the U.S. microelectronics sector and supply chain amid unprecedented regulatory change.

Michael MillerTrade Manager, Global Trade Compliance, Empowered OfficialFlex

Matt SilvermanGlobal Trade Director and Senior CounselVIAVI

Joseph StoneSenior Export Controls Manager, IT & DigitalRolls-Royce (UK)

Cristina Brayton-LewisPartnerWhite & Case LLP
- Gap analysis: Changes in DDTC/BIS insights into compliance monitoring
- Working in silos versus working as a whole
- Road map for a written compliance plan to cultivate a culture of compliance
- Touchpoint inventories: A holistic review of operations and where third-party data is stored and how it is screened
- Working with verified entities – How much due diligence is enough?
- Delve into certain components that companies have integrated within their current processes
- Industry specific challenges – Semiconductor companies, telecommunication companies, aerospace companies, O&G, etc.
- How to manage your compliance program with remote employees
Close of Day One
Day 2
May 16, 2024
Implementation of the Latest Wassenaar Arrangement Decisions: Global Efforts in Streamlining the Information Security Control List

Dr. Torbjörn GustavssonCrypto MathematicianFRA - Försvarets radioanstalt (Sweden)
- Ancillary encryption and the removal of a grey exception
- Challenges with mixing exceptions for items and functions
- Possible key limits on post quantum algorithms?
- The past and the future of OAM encryption
Cloud Computing, End-Use Controls and Technology Transfers: Navigating the Grey Areas of 734.20/734.18 Exemptions and Beyond

Tansie Taylor IwafuchiSenior Manager, Export Controls, Global Trade ComplianceMicrosoft

Thoth V. WeedaCompliance CounselBentley Systems
The definition of “export” in the EAR and ITAR both include the concept of releasing technical data or technology to a foreign person in the U.S. as part of the definition of a “deemed export”, or the transfer of ownership or control of a technology to a foreign person. Interesting changes are proposed – §734.18 and 734.20 – to the EAR, and – §120.52 – to the ITAR, which would deal with transfers of technology and use of encryption. What’s behind these rules, what are the limitations, and how is industry is managing these exceptions?
Networking Break
Unlocking EAR Treatment of Software Releases and Access Information Transfers: Navigating 734.15 / 734.19 and the Encryption Nexus

Bob BowenExport and Trade Compliance CounselServiceNow

Michelle AragonSenior Manager, Trade ComplianceLeonardo DRS
In September 2023, the BIS amended EAR provisions on the release of software and access information related to software. These amendments have changed the EAR landscape related to the concept of release as that term applies to software and related access information. This panel will examine these changes and the impact that they have on software-related activities subject to the EAR.
Networking Luncheon

Jai Singh ArunHead of IBM Quantum Safe Product Management & StrategyIBM

Yvonne Brye-VelaData Security and PrivacyGoogle;
Adjunct Professor, San Francisco State University
With quantum computers advancing rapidly, traditional security protocols face a significant threat as they can be easily compromised. In this session, we will explore the importance of quantum-safe cryptography to safeguard sensitive data in the age of quantum computing.
The Commercial Spyware EO and Finding the Right Balance Between Offensive and Defensive Cyber Security Policy
David KovarFounder and CEOURSA Inc.

Roszel C. Thomsen IIPartnerThomsen and Burke LLP
An offensive security strategy aims to preemptively identify and mitigate gaps and weaknesses within an organization’s digital infrastructure. Defensive cybersecurity involves a systematic and comprehensive approach to identifying vulnerabilities and weaknesses before they can be exploited. With the Commercial Spyware EO in place, is the EO too defensive/restrictive, creating negative economic implications? How can the U.S. find the right defensive/offensive cyber-stance?
Networking Break
Around the World in Encryption: The Latest Developments Coming Out of the EU, Russia, China, Japan and Israel

Yan LuoPartnerCovington & Burling (China)

Brian J. EganPartnerSkadden, Arps, Slate, Meagher & Flom LLP

Doron HindinAssociate General Counsel, International TradeMcKinsey & Company (Israel)
Part One: China and Japan
- China’s Commercial Encryption Regulations: Criteria inclusions for obtaining applicable certifications, qualifications, and licenses
- Japan’s The Protection of Personal Information Act No. 57 of 2003 (APPI): Guidelines for specific sectors, including financial, medical and telecommunications
Part Two: EU and Russia
- EU proposals to require mass data scanning, compromising end-to-end encryption
- Russia
- Impact of encryption controls on Russia “exit” transactions
- Availability of exemptions and licenses for encryption activities in Russia
Part Three: Israel
- The MOD Encryption Control Department’s initial licensing processes
- Government-private sector collaboration
AUDIENCE POLLING
Closing Roundtable Discussion: The Next Phase of Encryption, Cloud and Cyber Export Compliance for 2024 and Beyond
This interactive, brainstorming session will take stock of the greatest compliance risks, emerging issues, and global regulatory dynamics that will impact compliance programs in the short, medium and long term.
